|
NetBurner 3.5.7
PDF Version |
|
NetBurner 3.5.7
PDF Version |
This guide describes the PC tools and utilities that run as stand-alone programs, as well as automatically as part of the NetBurner development tools suite. The executable version of the tools are located in \nburn\pcbin, and the source code is located in \nburn\pctools.
Multi-Threaded TTY (MTTTY) is a serial terminal utility that you can use to communicate with the RS-232 serial ports on your NetBurner device or development kit. It is multi-threaded in that you can run multiple instances of MTTTY for each serial port.
MTTTY is commonly used for:
MTTTY can be started from:
\nburn\pcbin\mttty.exe 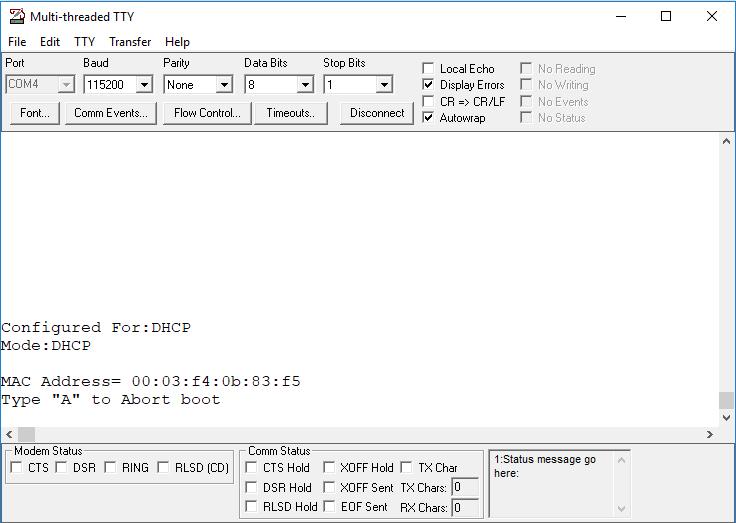
Primary method to program an application into a NetBurner device by posting the application file to the device's config server. It is used automatically by both NBEclipse and the Makefile command line tools. The default flags to call wget are as follows: wget -nv -O- --progress=dot:micro --post-file=<file name> <Device IP>:20034/appupdate.htm
Wget also supports loading code onto a device that has been protected by username/password authentication. On the command line, the device username and password are configured by setting the environment flags NBUSER and NBPASSWORD. For example, in a make load, set the username and password as follows: make load NBUSER=foo NBPASSWORD=bar. In NBEclipse, username and password are set via the project options. Right click on a project and select Properties. Username and password text input boxes can be found under NetBurner Options. Finally, if manually utilizing wget, use the following wget flags to set a username and password: --user=foo --password=bar.
Alternative method used to program an application into a NetBurner device by posting the application file to the device's config server. It is invoked as part of the make system for NetBurner development kit NBEclipse and command line builds. It can be replaced with WGET. The format is nbupdate <file name> <device IP>
While smart traps is not a specific PC application, the interface is accomplished by running the MTTTY serial terminal. During software development it is possible for a software developer to download an application with a coding error severe enough to cause an application to crash. Common causes of a system crash are: task stack overflow, indexing an array out of bounds and bad pointer assignments. When a system crash occurs a device will usually recover by a reboot of the system. The purpose of the SmartTrap utility is to provide more information about the system when the crash occurred to assist with debugging the problem. Smart traps are automatically enabled by the init() function. Note that smart traps are disabled when building an application in debug mode.
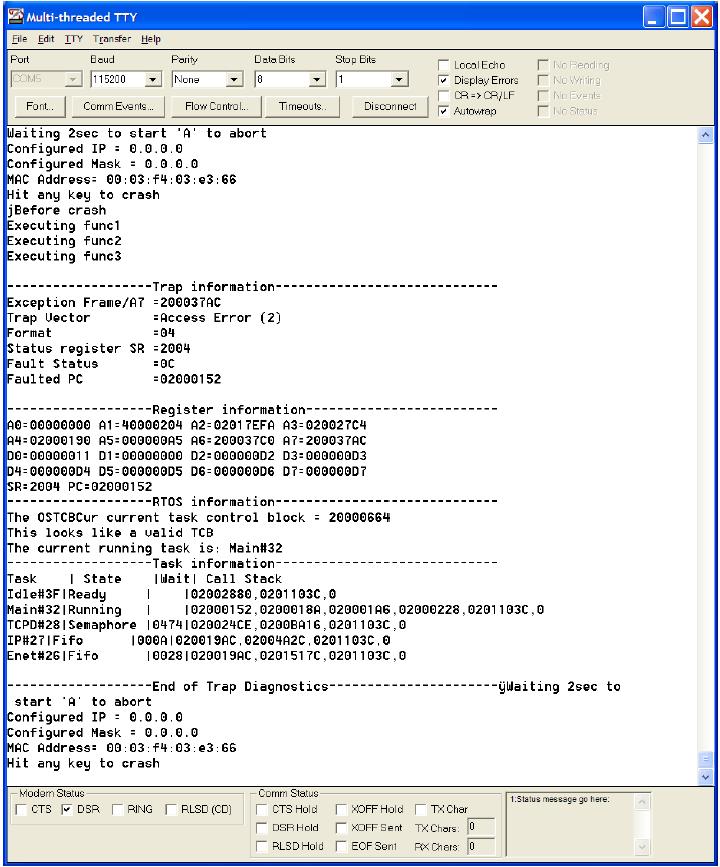
\nburn\docs directory of your development tools installation. This section displays the processor status and error registers. The most significant is the Faulted PC, with is the Program Counter register indicating the area where the fault occurred. In this example the program counter value at the time a trap was detected is 0x02000152.
This section displays the processor's Address and Data registers.
Identifies the RTOS Task Control Block and the current running task. The priority number is in hexadecimal. Traps caused by stack overflows may corrupt this section of the report.
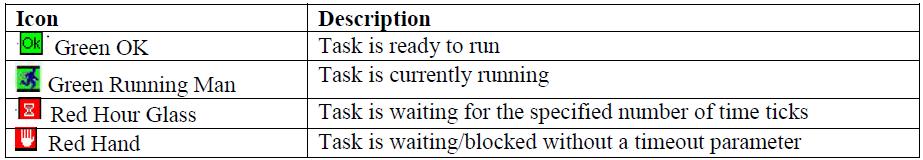
This is a very useful section of the report. It identifies each task, as well as its current state, wait time, and call stack. If you look at the Main task, you can see 6 entries with 0x02000152 (the faulted pc) at the left, and 0 at the right. The value of 0 is the start of the call stack. Each hexadecimal address between those two numbers represents each function that was called.
Each address can be related to the corresponding line number in the source code by using the WinAddr2Line utility. By selecting the .elf file location and each address in the call stack you can determine the calling sequence starting from 0 on the right and moving to the left. The last line signifies the end of the SmartTrap output. Since the boot monitor is configured to "boot to application", the device reboots after the trap occurs.
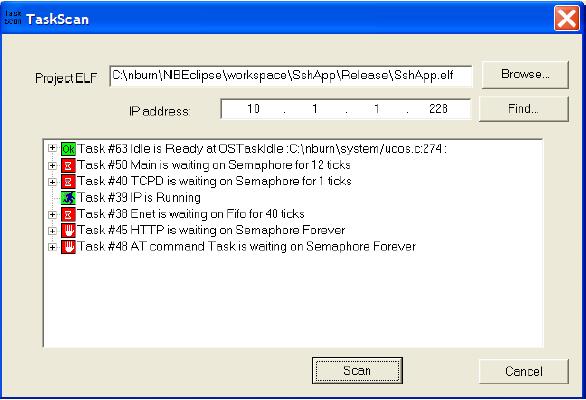
TaskScan is an network connected debugging tool that can be used to view the RTOS tasks and status of your running NetBurner application. This tool is unique in that it is active in the release build of your code, rather than the debug build which is compiled without optimization. It is very useful to determine such things as why a specific task is not running the way you had anticipated, if it is waiting on other tasks, and its call stack. TaskScan is only active when the PC program generates a request, so it will not impact your release code execution speed otherwise.
The init() function will automatically include taskmon.h and call EnableTaskMonitor(). TaskScan requires that you have the Executable and Linking Format (ELF) file for the specific application that is running on your NetBurner device. The .elf file is created by the compiler each time you build your application. It contains information TaskScan needs to link the application executable to the source code and task information. For example, if you have a project named MyProject, a file named MyProject.elf will be created.
TaskScan is commonly used for:
TaskScan can be started from:
\nburn\pcbin\taskscan.exe 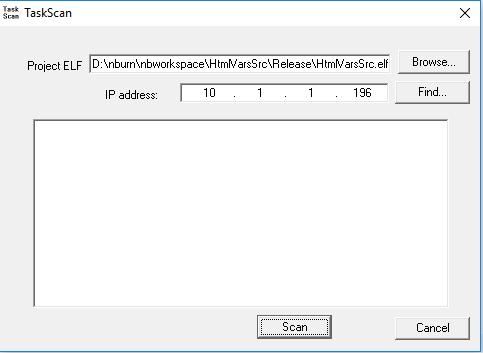
WinAddr2Line only works for ColdFire-based platforms. For ARM, see Addr2line
Utility to determine the source code location for a specified memory address and .elf file. This application is typically used in conjunction with the SmartTraps utility when debugging an application that is crashing.
WinAddr2Line is commonly used for:
WinAddr2Line can be started from:
\nburn\pcbin\winaddr2line.exe. 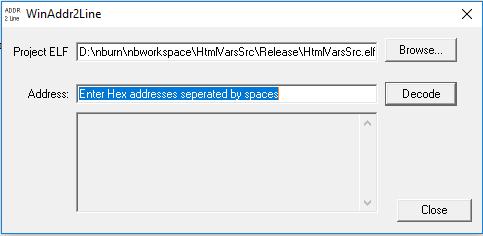
The Windows IPSetup utility was used for network configuration in releases prior to 3.x. Network configuration is now down through the network configuration server on the NetBurner device. See Device Discovery and Configuration and Config Server Programming Guide for documentation on the 3.x network configuration system.
Autoupdate was used for loading applications to a device in releases prior to 3.x. Updating code is now done through the configuration server, nbupdate utility, or WGET.
The virtual comm port driver for Windows creates a virtual serial port and associates it with a network IP address and port number. It is typically used for legacy Windows applications without the ability to communicate over a network.
This utility is used by the NetBurner make system. It takes the contents of a project's html directory, implements the NetBurner dynamic web content scheme, callbacks, variables, access priorities, and mime types, and creates a file named htmldata.cpp.
This utility is used by the NetBurner make system for 5441x platforms. It processes a .s19 file into a compressed binary with checksum and header.
This utility is used by the NetBurner make system for ARM platforms. It processes the application.elf file into a compressed binary with checksum and header.